Beginner’s guide: OSSIM Part 2

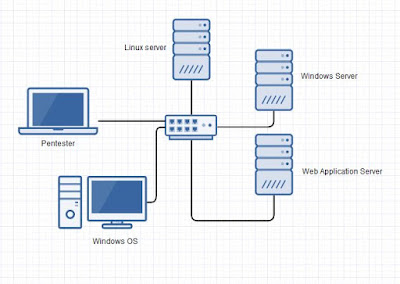
Hope all of you are keeping well. Thank you all for the overwhelming support you people are giving me. So today we’ll deal with everything from basic OSSIM configuration to integrating different types of assets. Before we jump in to all of that I hope all of you are ready with installation. If not please visit my previous post, which is actually the first part. Beginner’s guide: OSSIM (Open Source Security Information Management) part 1 Make sure you have an active internet connection for your OSSIM. As you all know the Alienvault platform has five modules in it, which are the Asset discovery, vulnerability assessment, threat detection, behavioural monitoring and security intelligence. In simple words we add assets first, and then we’ll configure all those assets under each and every module of Alienvault respectively. If you're ready with everything mentioned in part 1, we can now move forward with the configurations. Here we’re just considering only OSSIM not USM....